Two Russians, Two Schemes, One Message: American Justice Has a Long Memory
 Photo by Tima Miroshnichenko
Photo by Tima Miroshnichenko
The Ransomware Assembly Line
Most people imagine a hacker as one person — a lone figure hunched over a keyboard, picking locks in the dark. The reality of modern cybercrime is far less romantic and far more dangerous. It looks less like a lone wolf and a lot more like a franchise — with specialists, suppliers, middlemen, and paying customers, all working in coordinated layers to squeeze money out of American businesses and families.
This week, two federal courtrooms — one in Indianapolis, one in Detroit — delivered sentences to two Russian nationals whose cases, taken together, reveal exactly how that criminal assembly line works, and what it costs its victims.
Case One: The Door Opener — Aleksei Volkov
Aleksei Volkov, 26, of St. Petersburg, Russia, was sentenced to 81 months — nearly seven years — in federal prison for assisting major cybercrime groups, including the notorious Yanluowang ransomware group, in carrying out attacks against U.S. companies and organizations, causing over $9 million in actual losses and over $24 million in intended losses.
Volkov’s role in the cybercrime ecosystem had a specific job title in the underground world: Initial Access Broker. It is worth understanding what that means, because it is a growing and critical part of how ransomware attacks happen.
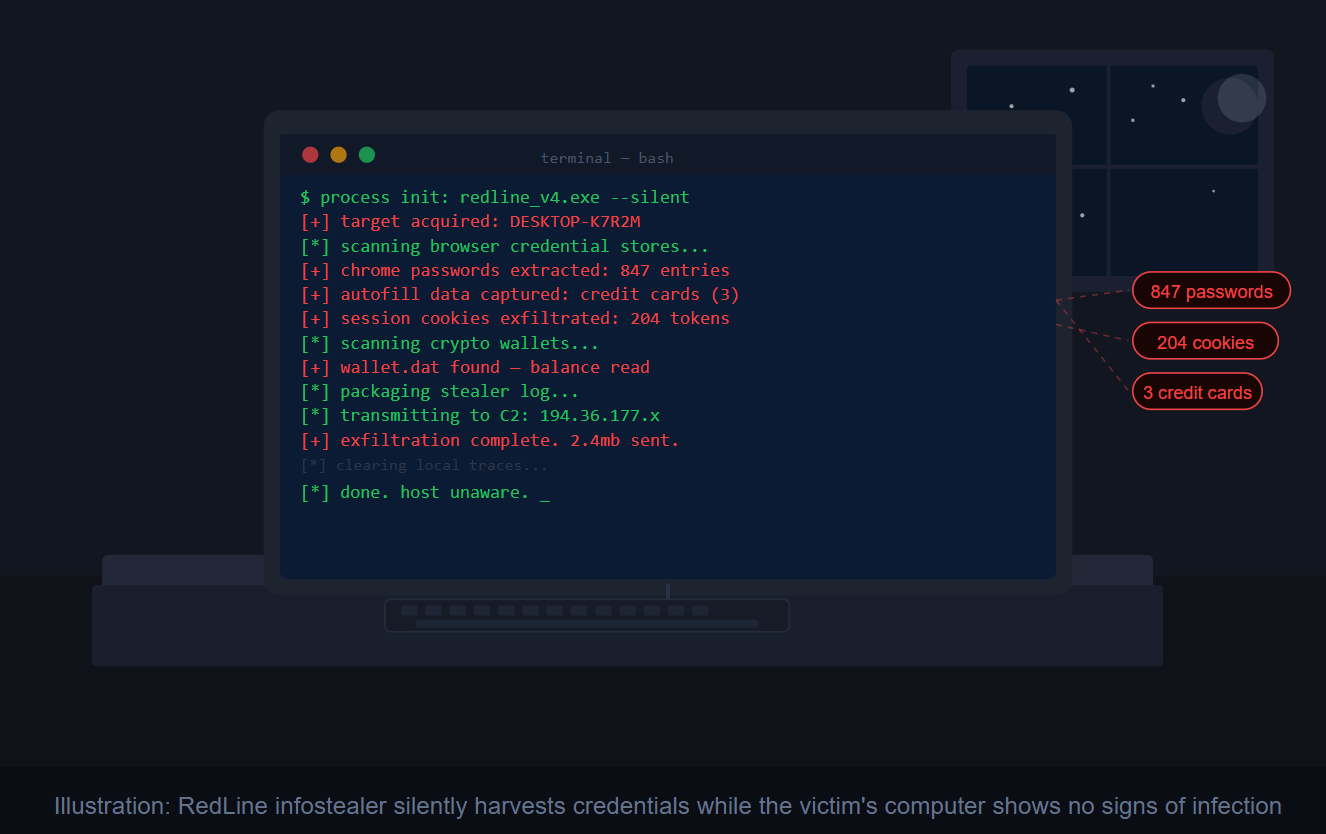
An initial access broker is a specialist who focuses on gaining unauthorized access to corporate computer networks and systems — and then selling that access to other cybercriminals rather than exploiting it directly. Think of him as a burglar who breaks into a building, props open the back door, and then rents out that open door to whoever wants to come in next.
Volkov’s buyers were ransomware groups. Once inside the networks he had unlocked, they deployed malware that encrypted the victims’ data, locked them out of their own systems, and demanded payment in cryptocurrency — sometimes in the tens of millions of dollars — in exchange for restoring access. In some cases victims paid. In others, the criminals followed through on their threat and dumped stolen confidential data on public “leak” websites for the world to see.
Volkov agreed to pay full restitution of more than $9.1 million to known victims and to forfeit the equipment he used to carry out his crimes. He was arrested in Rome, Italy and extradited to the United States, where cases originally filed in both Indiana and Pennsylvania were consolidated for sentencing.
Case Two: The Zombie Army Builder — Ilya Angelov
The second case, out of Detroit, reveals a different but equally essential piece of the ransomware puzzle: the botnet.
Ilya Angelov, 40, of Tolyatti, Russia — who used online aliases including “milan” and “okart” — was sentenced to 24 months in prison and fined $100,000, with a money judgment of $1.6 million entered against him.
Angelov co-managed a Russia-based cybercriminal operation that the FBI designated as “Mario Kart” — a name that belies the genuine damage it inflicted.
So what exactly is a botnet? Imagine thousands of ordinary home and business computers — belonging to regular people who have no idea anything is wrong — quietly infected with malware and secretly controlled by criminals overseas. Each infected machine is a “bot.” Together, they form an army the criminals can point at any target they choose.
Angelov’s group built their botnet by distributing malware-infected files attached to spam emails. They then monetized the botnet by selling access to individual compromised computers to other criminal groups, who used that access to launch ransomware attacks — locking victims out of their networks and demanding cryptocurrency payments to restore access.
The scale of damage is staggering. The FBI identified over 70 U.S. corporations that were infected with ransomware by one organization linked to Angelov’s group alone, resulting in over $14 million in extortion payments. A separate ransomware group paid Angelov’s operation more than a million dollars just for access to the Mario Kart botnet.
The Criminal Supply Chain — Explained
Taken together, these two cases are a textbook illustration of how the modern ransomware economy operates. It is not one criminal doing everything. It is a supply chain:
- Botnet operators (like Angelov) infect thousands of computers and sell access to the highest bidder.
- Initial access brokers (like Volkov) probe corporate networks for weaknesses and sell a way in.
- Ransomware groups (like Yanluowang) purchase that access, deploy their encryption software, and collect the ransom.
- Money launderers convert the cryptocurrency proceeds into untraceable cash.
Each player is a specialist. Each gets a cut. And American businesses — hospitals, schools, manufacturers, and local governments — are the ones left holding the bill.
What This Means for You
You may not run a corporation, but this criminal ecosystem affects everyone. Ransomware attacks on hospitals delay surgeries. Attacks on school districts expose children’s records. Attacks on local utilities and supply chains raise prices for everyone.
The good news is that both of these sentences — handed down just one day apart — demonstrate that U.S. law enforcement takes these crimes seriously regardless of where the criminals live. The FBI investigated Volkov’s case with assistance from law enforcement in Italy. justice The Justice Department’s Office of International Affairs provided critical assistance in the Angelov case as well. justice The arm of American justice, it turns out, reaches a very long way.
As for what you can do: keeping your devices updated, never opening unexpected email attachments, and using strong unique passwords remain your best personal defenses against becoming an unwitting link in someone else’s criminal chain.
Stay safe out there, and I’ll see you next week!
Feeling lost in the digital world? Dr. Tom is here to help!