The Password Thief: How a Global Malware Empire Ended in an Austin Courtroom
A Digital Heist Years in the Making
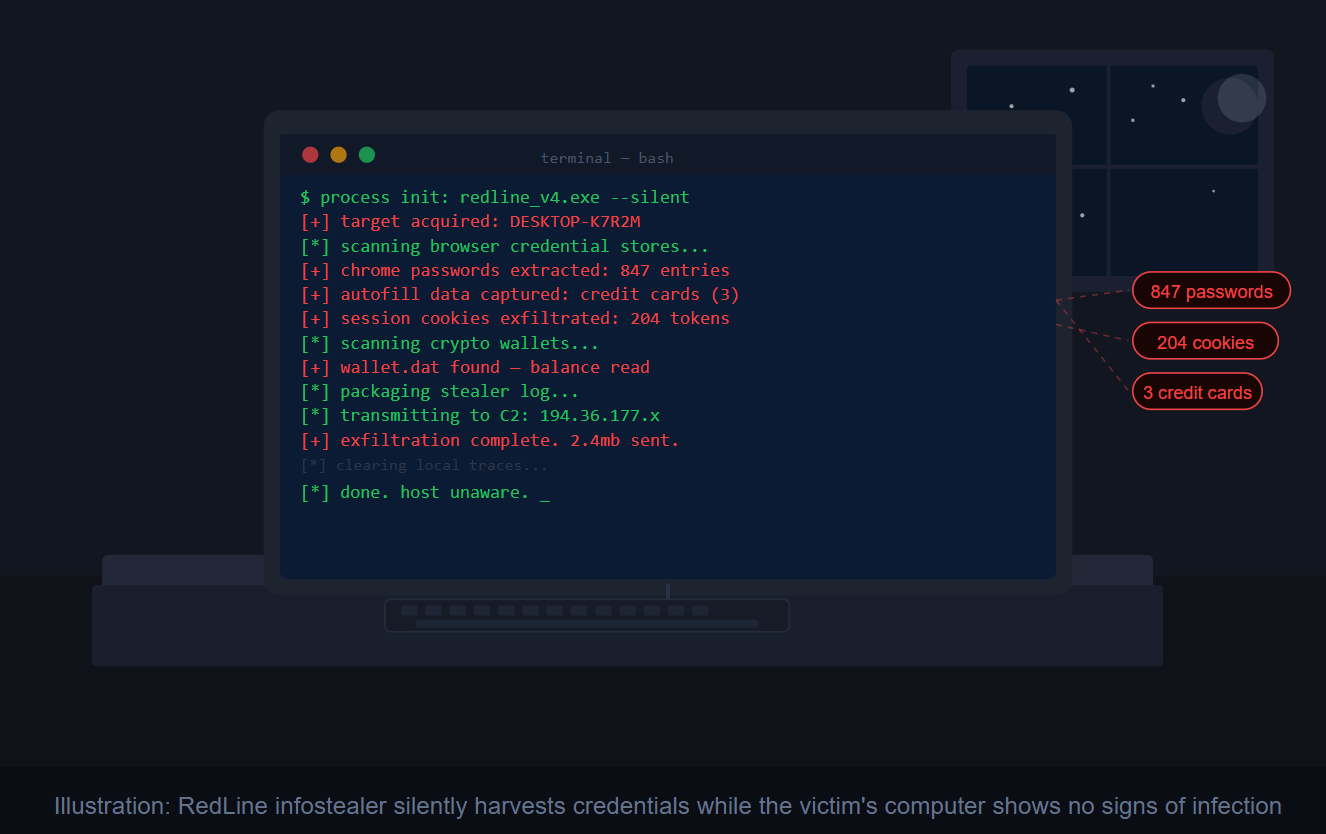
Imagine a burglar who never breaks a window or picks a lock. Instead, he quietly slips into your home while you’re asleep, photographs every key on your keyring, copies down your bank account numbers, snaps a picture of your credit cards, and is gone before morning — leaving no trace. You won’t know anything is missing until weeks or months later, when your accounts start going dark one by one.
That is almost exactly what a piece of software called RedLine Infostealer does — and this week, one of the men allegedly behind it took his first steps into an Austin, Texas federal courtroom.
Who Is Hambardzum Minasyan?
On March 25, 2026, the U.S. Attorney’s Office for the Western District of Texas announced that Hambardzum Minasyan, an Armenian national, had been extradited to the United States to face federal charges for his alleged role in one of the most widespread malware operations in recent history.
According to court documents, Minasyan allegedly conspired with others to develop and administer RedLine — one of the most prevalent infostealing malware variants in the world, previously used to conduct intrusions against major corporations. justice
The three-count indictment charges him with conspiracy to commit access device fraud, conspiracy to violate the Computer Fraud and Abuse Act, and conspiracy to commit money laundering. If convicted, he faces up to 10 years in prison for access device fraud and up to 20 years for each of the other two counts. justice
What Is an “Infostealer” — and Why Should You Care?
Most people picture computer viruses as something dramatic — a flashing warning screen, a locked computer, a ransom demand. RedLine works nothing like that. It is quiet, fast, and devastatingly effective.
RedLine is a malicious information-stealing program that uses a customizable file-grabber to collect victims’ sensitive data from web browsers, applications, messaging apps, and cryptocurrency wallets. NordVPN In plain English: the moment it lands on your computer, it goes to work harvesting everything your browser has been helpfully saving for you — your usernames, passwords, credit card numbers, and autofill data.
It also steals browser cookies, including session cookies that can bypass multi-factor authentication. ExpressVPN That last detail is chilling. Even if you use two-factor authentication — something Dr. Tom has strongly encouraged in a previous column — a stolen session cookie can let a criminal walk right past it, because as far as the website is concerned, it looks like you are already logged in.
According to Kaspersky research, RedLine was used in 51% of all infostealer infections between 2020 and 2023 Flare — making it, at its peak, the single most dominant password-theft tool on the planet.
The “Malware-as-a-Service” Business Model
Here is what makes this case especially significant: Minasyan and his co-conspirators weren’t just using RedLine. They were allegedly running it like a business.
Rather than being centrally operated, RedLine ran on a malware-as-a-service model in which anyone could buy a turnkey infostealer solution from various online forums and Telegram channels. We Live Security Think of it like a criminal franchise. The operators maintained the software, kept the servers running, and collected subscription fees. The “affiliates” — essentially paying customers — deployed the malware against whoever they chose and kept the stolen data.
The indictment alleges that the conspirators maintained digital infrastructure — including command-and-control servers and administrative panels — to enable affiliates to deploy the malware, collected payments from those affiliates, and laundered the criminal proceeds through cryptocurrency exchanges. justice
Minasyan’s specific role, according to prosecutors, included registering servers to host RedLine’s infrastructure, setting up online file-sharing repositories used to distribute the malware to paying customers, and creating a cryptocurrency account to receive payments — all allegedly beginning as early as 2021.
How the Long Arm of the Law Caught Up
This arrest didn’t happen overnight. In October 2024, the Department of Justice joined the Netherlands, Belgium, Eurojust, and other international partners in a coordinated disruption effort against RedLine — an operation that also unsealed charges against alleged co-conspirator Maxim Rudometov, described as one of the developers and administrators of the malware. justice
Minasyan’s extradition from Armenia to the United States on March 23, 2026 — just days before his court appearance — is a testament to what law enforcement can accomplish when countries work together. The investigation involved the FBI Austin Cyber Task Force, which included the Naval Criminal Investigative Service, IRS Criminal Investigation, and notably, the Defense Criminal Investigative Service (DCIS) — the same agency where Dr. Tom spent a significant part of his career.
How to Protect Yourself from Infostealers
RedLine and its successors typically land on victims’ computers through phishing emails, fake software downloads, and malicious ads. In some cases, victims download the malware thinking they are getting new antivirus software or an operating system update. NordVPN Here is how to stay protected:
- Never save passwords in your browser. This is RedLine’s primary hunting ground. Use a dedicated password manager like Bitwarden or 1Password instead — these store credentials in an encrypted vault, not in an easy-to-grab browser file.
- Be skeptical of free downloads. Cracked software, free game cheats, and pirated applications are a common delivery method for infostealers. If it seems too good to be free, it probably is.
- Keep your antivirus updated. Modern antivirus tools can detect and block many infostealer variants before they execute.
- Watch for unusual account activity. If your email, social media, work, or shopping accounts show new logins, unfamiliar session alerts, or password-reset emails you did not request, take it seriously VeePN — it may be a sign your credentials are already in criminal hands.
The Minasyan case is a reminder that the cybercrime ecosystem is an organized, profit-driven industry — not the work of lone wolves in dark basements. But it is also proof that those who build these criminal empires eventually answer for it, even halfway around the world.
Stay safe out there, and I’ll see you next week!
Feeling lost in the digital world? Dr. Tom is here to help!










